In Part 1 of this series we looked at how we can report on missing driver updates for HP workstations using Intune Proactive remediations, Azure Log Analytics and Power BI. In Part 2 we’ll look at how we can deploy driver updates to devices and use the information available in the Power BI report to do granular targeting.
BIOS Updates
First a disclaimer that this solution does not install BIOS updates. You can report on them but not install them. The reason is there are, in my opinion, better ways to do that. BIOS updates can be installed with Windows Update for Business with a reasonably good experience, and with the commercial driver and firmware servicing controls you can be granular in your targeting and decide which updates can be deployed when and to whom. HP Connect also appears to be a great solution for updating BIOS in a controlled way (although I haven’t used it myself). Both of those methods used signed update files which avoids the need to deal with BIOS authentication, eg passwords or HP Sure Admin. In all honesty, it would be great if the HP Connect solution could also do other driver updates as well as reporting – then we’d have a one-stop shop for all kinds of HP updates.
Driver Update Script
The driver update script (download here) can be used to install applicable driver updates to your workstations. It is intentionally flexible and supports different run modes, such as:
- All – install all applicable driver updates for the device. This includes drivers, software and firmware updates.
- CriticalOnly – install only applicable drivers marked by HP as critical.
- SpecificCategories – install only applicable updates in a specific category or categories, including drivers, software and firmware
- SpecificUpdates – install only specific applicable updates by specifying the SoftPaq number/s
With this flexibility you can create multiple deployments targeting different groups of devices with different updates according to your needs.
To configure the script, you’ll need to set a few parameters in the Parameters section at the top.
- UpdateRunType. Choose from All, CriticalOnly, SpecificCategories, SpecificUpdates as described above.
- Categories. Only applicable for the SpecificCategories run type. Choose from Firmware, Software, Driver.
- SoftPaqNumbers. Only applicable for the SpecificUpdates run type. Enter the SoftPaq number/s for the updates you want to deploy.
- WorkspaceID. The ID of your Log Analytics workspace, which you can get from the Overview page.
- PrimaryKey. The primary key of your Log Analytics workspace, which you can get from the Agents page.
- LogName. This is the name of the custom table that will be created in the Log Analytics workspace. This will be suffixed with “_CL” when created as for all custom logs. Note that the PowerBI report expects to use the parameter value that is already present in the script, so if you change it you’ll need to also change the data source query in the report.
- ParentFolderName. This is the name of the folder that will be created on the local machine under %ProgramData% and in the registry under HKLM:\Software.
- ChildFolderName. This is the name of the subfolder that will be created underneath the parent folder.
- InstallTimeout. The maximum number of minutes to wait for an update to install. Used as a safeguard should something go wrong with the installation.
- MinimumFrequency. This value, in hours, simply sets a gate that prevents the script from running too frequently, as can be the case with PR scripts that can attempt to run multiple times in different user contexts, even with a one-time deployment.
What does the script do?
The script will create a working directory under %ProgramData% where it will download the HP Image Assistant and temporarily cache any downloaded updates.
It will use the HPIA to analyze the system for missing driver updates to make sure that only applicable updates get installed. Based on your selections it will download the update files and then silently install them. All updates are downloaded first, then installed after as some updates may disconnect the network temporarily.
Once all updates have been installed, it will post log entries with the installation results to your Log Analytics workspace so you can report on them.
The script also logs to the local machine. You can see an example of such a log file here (in CMTrace format).
Deploying the Script
Create a Proactive remediations script in Intune in the same way you did in Part 1, using only a Detection script. You may wish to schedule the script as a one-time deployment rather than a regular one, depending on your requirements.
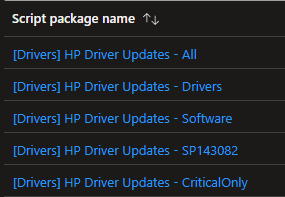
You can create multiple PR scripts according to your requirements, for example:
Self-Service
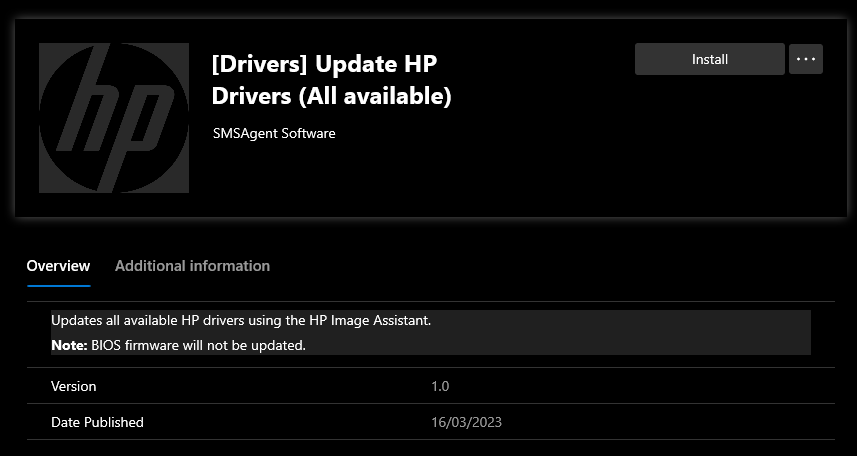
Another option is to self-service the script, ie package it as a Win32 app in Intune and make it available in the Company Portal.
The way I do this is to use a “dummy” detection method on the app which simply checks if the driver updates log was updated in the last 5 minutes. If so, the app is detected as “installed”. After 5 minutes, or when the app next evaluates, it will no longer be detected as installed and can be run again. In this way, the same app can be used to update drivers multiple times whenever the user wants.
You can find the detection script I use here. You’ll need to update the path to the driver updates log on your devices.
Targeting
You could simply target all your HP workstations to run the script installing all missing driver updates on a regular basis – a set and forget approach. Or if you want more control, or prefer to stage your update rollouts, you can use Intune filters and/or build Azure AD groups containing only the devices you want to target. Use the information provided in the Power BI report to decide which updates you want to deploy and which devices are applicable for targeting.
Reporting
You can download an updated version of the report we used in Part 1 here, which also includes an Update Install Log page. This additional page contains the installation results for driver updates posted by your workstations. You can view update installations in a timeline, filter by update status, update name, computer name or model. Bear in mind that the data is only kept in the Log Analytics workspace for the length of your data retention period so the data displayed in the report won’t be any older than that.
Configure the report in the same way you did in Part 1. Bear in mind you must have some data in both Log Analytics tables before you can configure the report.

Final notes
A few considerations before I sign off!
- Do be aware that some driver updates will disconnect the network temporarily. I have seen this not just with NIC or WiFi drivers, but also Intel firmware updates. To minimize the impact to users, you may want to schedule updates first thing in the morning when they first sign in rather than during the day when they may get disconnected from an important Teams meeting or something!
- Some driver installations report as “NOREBOOT” when in fact they do require a reboot. This is no fault of the solution; it’s just the way the HP SoftPaq installation logic is configured.
- Sometimes more than one driver update is installed by a single SoftPaq. For example, you may have a missing driver update reported in the “Software” category and another update in the “Driver” category but only one SoftPaq is needed to install both.
- For additional installation logging, have a look under %ProgramData%\HP\Logs and C:\SWSetup\<SPnumber>.
This is by far the best detailed script I’ve used. Everything is so detailed and easy to follow.
Thank you.
Awesome, glad it helps 🙂
Good Post, Trevor. One of my customers are looking to use your script for latest HP models. Does this script work on the latest HP models purchased for enterprise?.
Hey Prajwal, the script uses HP’s HPIA utility so will work on any model the utility supports. HP publishes a list here: https://ftp.hp.com/pub/caps-softpaq/cmit/imagepal/ref/platformList.html