When working with Microsoft Graph in PowerShell I tend to use the REST API directly rather than cmdlets provided by Microsoft in their Graph modules – just personal preference I suppose. I found myself needing to query the Windows Update for Business deployment service using the Graph API, and this requires a specific permission – WindowsUpdates.ReadWrite.All. To get an access token to work with Microsoft Graph I tend to use the following command, using the Intune PowerShell SDK, as it’s quick and easy:
$GraphToken = Connect-MSGraph -PassThru
However, the enterprise app for that PowerShell module doesn’t contain the required permission in its default delegated permission set. I don’t know why it took so long to figure this out, but to add the delegated permission I needed to use the Microsoft Graph PowerShell SDK (I believe the Application.ReadWrite.All permission is required for this.) The code below basically adds the permission as an “Oauth2 permission grant” on the app, and adds the additional WindowsUpdates.ReadWrite.All permission while retaining the existing permissions.
Connect-MgGraph -Scopes "Directory.AccessAsUser.All" -TenantId "<YourTenantId>”
Import-Module Microsoft.Graph.Identity.SignIns
$EnterpriseAppName = "Microsoft Intune PowerShell" # for Intune PowerShell SDK, or "Microsoft Graph PowerShell" for Microsoft Graph PowerShell SDK
$GraphSp = Get-MgServicePrincipal -Filter "AppId eq '00000003-0000-0000-c000-000000000000'"
$IntuneSp = Get-MgServicePrincipal -Filter "DisplayName eq '$EnterpriseAppName'"
$pgs = Get-MgOauth2PermissionGrant -All | Where-Object {$_.ClientId -eq $IntuneSp.Id}
$GraphPgs = $pgs | Where {$_.ResourceId -eq $GraphSp.Id}
$ExistingScope = $GraphPgs.Scope
$NewScope = $ExistingScope + " WindowsUpdates.ReadWrite.All"
$pgid = $GraphPgs.id
$params = @{
Scope = $NewScope
}
Update-MgOauth2PermissionGrant -OAuth2PermissionGrantId $pgid -BodyParameter $params
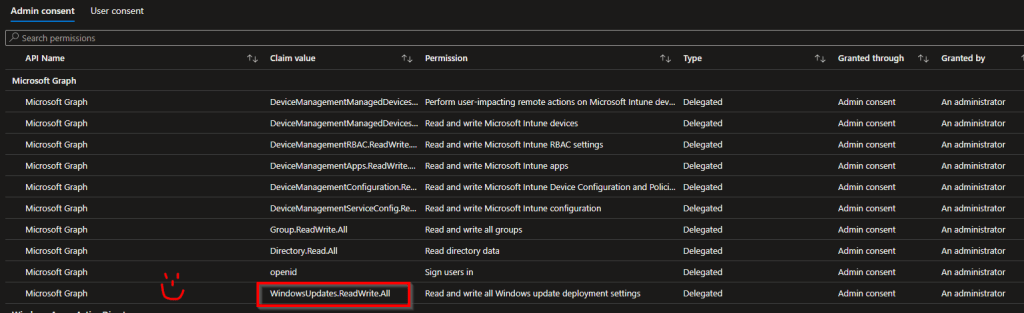
Note this only affects delegated permissions, not application permissions, which is a different thing.
Once the permissions are granted on the app, you also need the Windows Update Deployment Administrator Azure AD role to work with the WUfB deployment service.
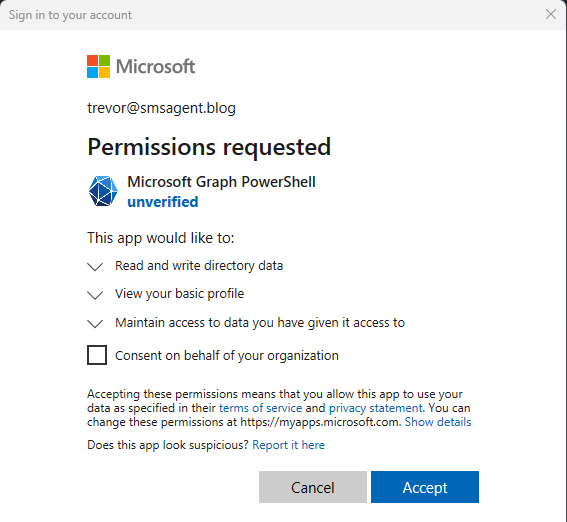
If you prefer an easier life (something I need to learn!!) you can just use the Microsoft Graph PowerShell module. To add the additional delegated permission, you can use the code above and just change the enterprise app name, or simply specify the permission as a scope when you connect – if you have the Global Admin role you can consent for your organization.
Connect-MgGraph -Scopes "WindowsUpdates.ReadWrite.All"
Then you can use the cmdlets in the Microsoft.Graph.WindowsUpdates module to work with the deployment service.