Yesterday I published a PowerShell script that retrieves activity log events for an Azure subscription. In this post, I will demonstrate how you could automate a daily email summary report of activities in your subscription using Azure automation.
The email report looks something like this, with a summary of operations performed over the last 24 hours and grouped by the calling identity, which could be a user, a service principal etc. If there is something specific you want more information on, you can then use the PowerShell script to find the details, which I’ll demonstrate as well.
Use a Managed Identity
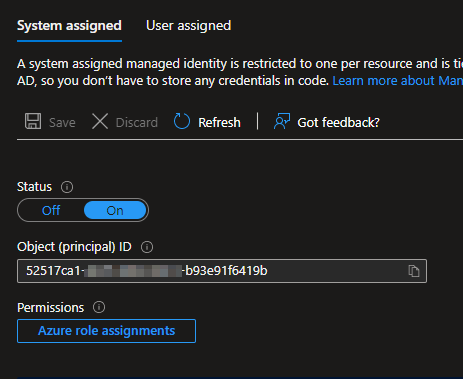
In your Azure automation account, make sure you have either a system or user assigned managed identity enabled. This allows you to authenticate without supplying credentials.
We’ll need to give the managed identity some permissions – to view the activity log in the subscription, as well as to Microsoft Graph to retrieve service principal information.
Create a custom role
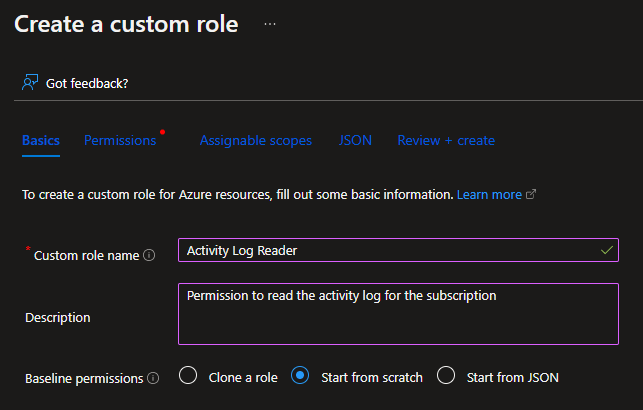
First, I recommend to create a custom role in your Azure subscription that just allows permission to read the activity log. In the Access control (IAM) pane of your subscription, select Add > Add custom role.
I’m calling the role Activity Log Reader. Choose the Start from scratch permission option.
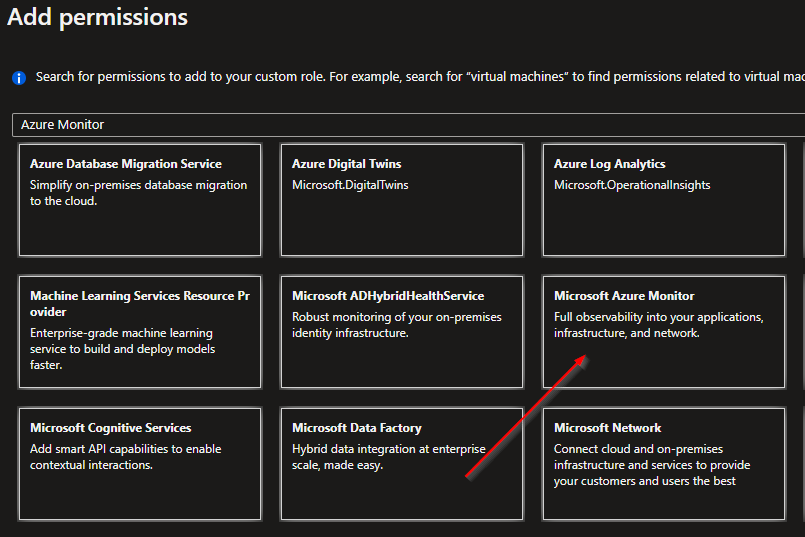
On the Permissions tab, click Add permissions. Search for the Microsoft Azure Monitor permission set.
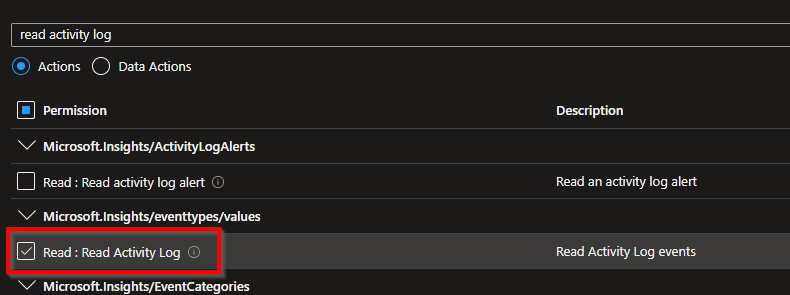
Search for and select the Read Activity Log permission, then click Add.
Click Review + create > Create.
Once created, we can assign our managed identity this role, either here or in the automation account. Since we’re here in the subscription, in the Access control (IAM) pane again, click Add > Add role assignment.
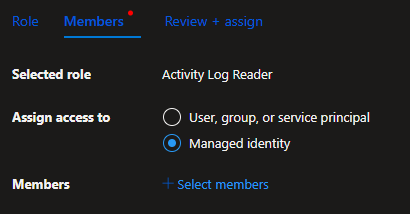
Select the Activity Log Reader role we just created, click Next,
Select Managed identity and click Select members
Select Automation Account and select the MI for the automation account
Click Review + assign.
Grant API permissions
Next we’ll need to grant API permissions to the managed identity so it can read service principals from Microsoft Graph. This does require a global administrator in Azure.
Follow the instructions here and the only permission needed is Directory.Read.All.
Create the Runbook
Create a new runbook in the automation account for PowerShell and the 5.1 runtime.
Paste in the content of this runbook script.
You’ll need to update some of the parameters at the top of the script, including your tenant Id, subscription Id, subscription name, and the email to, from and smtpserver parameters.
Save and start the runbook to receive your report, and don’t forget to set a daily schedule!
Investigating further
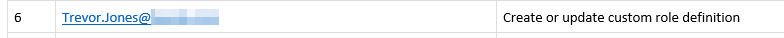
Let’s say you wanted to get further details on a particular operation that appears in the summary report. For example, in my own email report I see that I created a custom role definition, so let’s investigate that to find out what was created.
First, install the Get-AzSubscriptionActivityLog script from the PowerShell gallery:
Install-Script Get-AzSubscriptionActivityLog -Force
Then, if you’re not already authenticated with Azure in your session, run this with your subscription Id (Az.Accounts module required):
Connect-AzAccount -Subscription "<subscriptionId>"
Next, search the activity log for the relevant events (using the correct caller name of course!)
$ActivityLog = Get-AzSubscriptionActivityLog `
-TenantId "<tenantId>" `
-SubscriptionID "<subscriptionId>" `
-TimespanHours 24 `
-IncludeProperties `
-Caller "foo.user@contoso.com" `
-OperationName "Create or update custom role definition" `
-Status Started
The details I want to see for this event are in the additional properties, and in the requestbody property specifically, so let’s do this:
$Request = ($ActivityLog[0].properties.requestbody | ConvertFrom-Json).properties
$Request | fl
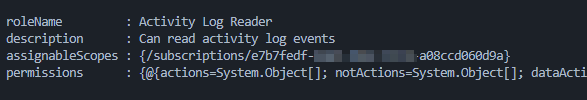
This shows me the Activity Log Reader role I created earlier:
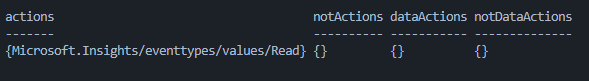
And if I want to see the permissions assigned to that role:
$Request.permissions